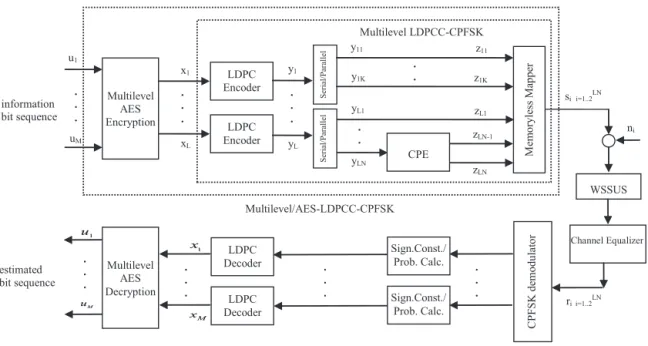
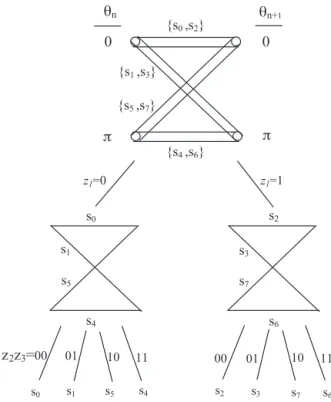
Multilevel/AES-LDPCC-CPFSK with Channel Equalization over WSSUS Multipath Environment.
Tam metin
Şekil

Benzer Belgeler
The power capacity of the hybrid diesel-solar PV microgrid will suffice the power demand of Tablas Island until 2021only based on forecast data considering the
Sultan Abdül’aziz, Cülusundan sonra ekseri günler tenezzühlerini icra etmek üzere geldiği Ihlamur kasrında, çok merakı olan pehlivan gü reşlerini, koç ve
Eviriciler paralel çalıştırılırken güç akışında devamlılık, aktif güç-frekans ve reaktif güç-gerilim düşüm yöntemleri ile eviricilerin optimal güç
In this study, effects of frequency shift keying modulation technique on charging times of RF energy harvesting were measured and investigated in detail.. An
1920 senesi ikinci kânu nun 23 üncü cuma günü darüfünun (Üniversi te) konferans snlonunda yapılan Pierre Loti ihtifali ve orada Süleyman Nazif merhumun
Bakırköy Tıp Dergisi, Cilt 9, Sayı 3, 2013 / Medical Journal of Bakırköy, Volume 9, Number 3, 2013 141. kullanımı; lökopeni, trombositopeni, aplastik anemi,
Tarayıcı sistem, manyetize edici sistemi demir örgünün üzerinde hareket ettirerek, bütün donatının algılanması için kullanılmaktadır.. Bu sayede manyetik alan
Rizosferde bulunan organik kirleticiler bitki kökleri tarafından salınan enzimler ya da mikrobiyal degradasyonun fitostimülasyonu (kirleticilerin, rizosferde bitki kök eksudatları
